Australian owned. Sydney hosted. Auditor-ready.
Distributors handle vendor agreements, partner pricing, end-customer consumption data, and in many cases data classified under government and regulated-industry contracts. A billing platform is a trust boundary. Here is how we treat that, in specifics.
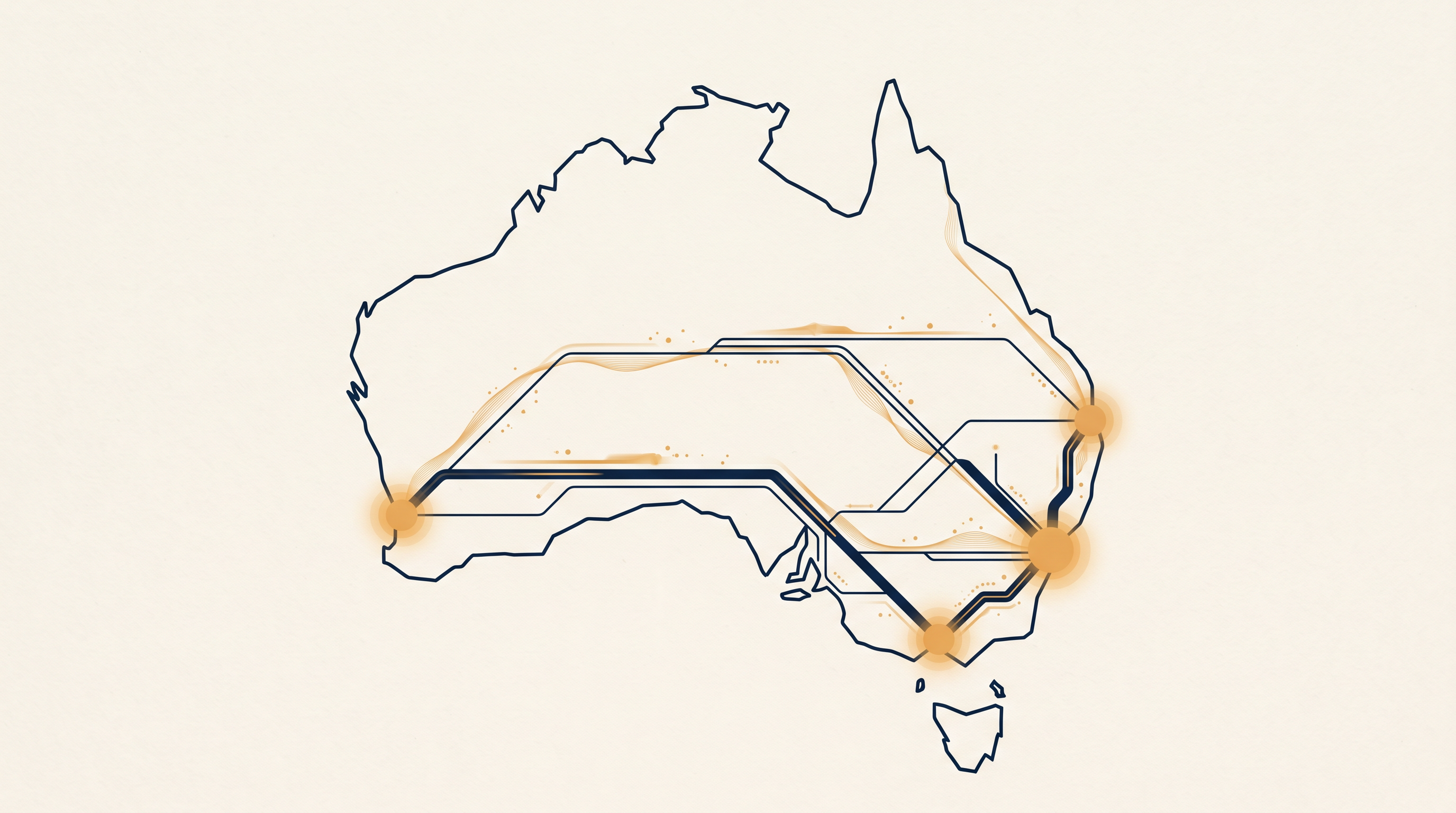
Where your data actually lives.
Primary hosting
AWS Sydney (ap-southeast-2). All production databases, application tier, object storage, and backups are provisioned in-region. We do not fail over to a non-AU region under any circumstance without the customer's written authorisation.
Support access
Support and engineering staff are based in Australia. Remote access to production data is audited, time-bound, and brokered through a session-level approval workflow. No offshore tier-one desk, no follow-the-sun 24/7 where an operator in another jurisdiction can open a partner's ledger at 3 AM.
No cross-border re-routing
We do not route customer data through US-parent tooling, observability pipelines, or shared-service infrastructure outside AU. Our logging and monitoring stack runs entirely in ap-southeast-2.
Your data stays yours
Customers own their data. Export is full-fidelity, not a sanitised report pack — you can take your ledger, your price sheets, your reconciliation history, your partner records. Termination does not hold data hostage.
Frameworks, direct.
ISO/IEC 27001
Our ISMS is designed and operated to ISO/IEC 27001:2022 controls. We are aligned today and on a scoped certification path with an external auditor. Stage 1 audit is in progress; we publish our SoA under NDA on request.
IRAP path
For customers serving Australian government or regulated-industry partners, we have scoped an IRAP assessment against OFFICIAL: Sensitive. Timeline and documentation packet available under mutual NDA.
Essential Eight alignment
We map our controls to the ASD Essential Eight, maturity level 2 targeted. Patch management, application control, MFA for admin, privileged access management, backup restoration testing — all in place and evidenced.
Privacy Act & notifiable breaches
We are an APP entity and operate under the Privacy Act 1988 and the Notifiable Data Breaches scheme. Breach response runbook, OAIC notification templates, and customer-communication protocol are documented and rehearsed.
What's actually in place, day one.
Encryption
- TLS 1.3 in transit, AWS-managed or customer-managed KMS keys at rest
- Per-tenant row-level isolation in the database; hard separation between customer ledgers
- Backups encrypted with dedicated keys; key rotation on annual cadence
Authentication
- SSO via SAML 2.0 or OIDC (Microsoft Entra, Okta, Google Workspace)
- MFA enforced for admin users regardless of IdP
- SCIM 2.0 provisioning for user lifecycle
- Partner portal has its own scoped authentication — never shared with the admin console
Access & audit
- Role-based access control with per-tenant scoping
- Full audit log of every admin action, 400-day retention
- Read-only auditor role for external review
- Exportable audit trail for SOX/SOC customers
Resilience
- Multi-AZ deployment in ap-southeast-2
- Point-in-time recovery, 35-day window
- Quarterly disaster-recovery exercise, documented RTO/RPO
- Backup restoration is tested, not just scheduled
What we'll hand them.
Procurement and risk teams ask the same 40 questions. We've answered them all. Under NDA, we make the following available in a single package:
- Information Security Management System (ISMS) summary
- Statement of Applicability (SoA) against ISO/IEC 27001:2022
- Penetration test executive summary (annual, independent)
- SOC 2 Type II when available; interim attestations in the meantime
- Privacy Impact Assessment template, completed for the platform
- Data flow and data residency diagram
- Breach response runbook and notification templates
- Subprocessor list and DPA
If your auditor has a specific question that isn't covered, ask. We'd rather give you a direct answer than a glossy security page.
"We're aligned, not certified, on X" is an answer we are willing to give where it's honest. "Certified as of <date>" is an answer we'll give where it's true. We don't hand out unsubstantiated compliance claims — distributors have real regulated customers, and a bluff gets you caught at the wrong moment.
Responsible disclosure
We run a coordinated disclosure programme. Report vulnerabilities to security@cloudbillingservices.com.au. We acknowledge within one business day, triage within three, and credit researchers on request. We do not threaten legal action against good-faith security research.
Get the security packet.
Send a short note and your NDA template. We'll return the full packet within two business days.